How To Repair Microsoft Hacked Computer
Hacking tool, which is a estimator program or software and helps a hacker to hack a reckoner system or a computer program. About people use 'Linux' for hacking equally it is the all-time open-source operating system. Simply what about windows users? Are you using windows and are searching for hacking tools? Here we have provided few hacking tools for windows users.
Although, there are not many hacking tools for windows that piece of work well here are some of the all-time hacking tools which perform hacking, security threat analysis, and penetration testing.

Summit 12 Hacking Software For Windows Users:
one. Metasploit – Penetration Testing Software:
It provides information on the vulnerabilities in the security system and performs penetration tests. Metasploit evades leading anti-virus solutions 90% of the fourth dimension and enables you to completely have over a machine yous have compromised from over 200 modules.

As a penetration tester, it pinpoints the vulnerabilities with Nexpose closed-loop integration using Pinnacle Remediation reports. Using the open-source Metasploit framework, users can build their own tools and take the all-time out of this multi-purpose hacking tool.
2. Acunetix Web:
Acunetix is a web vulnerability scanner (WVS) that scans and finds out the flaws in a website that could prove fatal. Past using Acunetix Web Vulnerability Scanner y'all tin can perform a full web scan from your computer in windows.
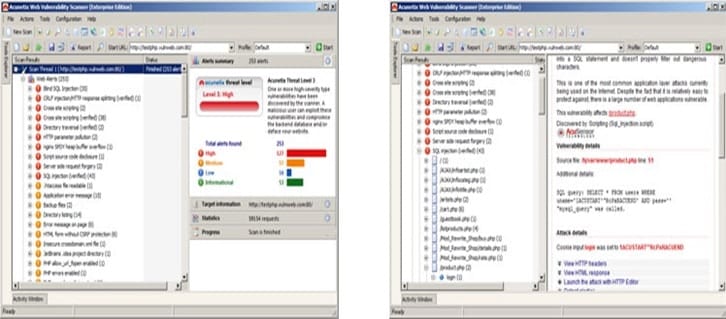
This is fast and like shooting fish in a barrel which scans WordPress websites from more than 1200 vulnerabilities in WordPress.
3. Nmap (Network Mapper):
Nmap (Network Mapper) is a port scanner tool. It is used to discover hosts and services on a figurer network. It is capable of Host Discovery, Port Scanning, Service Proper noun and Version Detection, OS Detection.

It is capable for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
4. oclHashcat:
Y'all might be aware of the free countersign peachy tool Hashcat. While Hashcat is a CPU-based password dandy tool, oclHashcat is the advanced version that uses the ability of your GPU. oclHashcat is the world'south fastest password cracking tool with the world's get-go and only GPGPU based engine.

For using this tool, NVIDIA users require ForceWare 346.59 or later and AMD users crave Catalyst fifteen.seven or after. It is released every bit gratis software and the versions available for Linux, Os 10, and Windows and tin can come in CPU-based or GPU-based variants.
5. Battlelog
Battlelog provides reliable and undetected hacks to competitive games such as Call of Duty, PUBG, Valorant, Overwatch, and GTA no name a few. The advantage of using cheats with them is that information technology is guaranteed to be prophylactic – which is very important if you are using game cheats to avoid getting banned or kicked out from the game.

6. Wireshark:
Wireshark is the world'due south foremost and widely-used network protocol analyzer.

Wireshark has rich features such as Deep inspection of hundreds of protocols, with more being added all the time, Multi-platform i.e; Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others. It monitors every unmarried byte of the information that is transferred via the network organisation.
7. Maltego:
Maltego is proprietary software used for open up-source intelligence and forensics, developed by Paterva. Information technology focuses on providing a library of transforms for the discovery of information from open sources and visualizing that information in a graph format, suitable for link assay and information mining.

It is a great hacker tool that analyzes the real world links between people, companies, websites, domains, DNS names, IP addresses, documents, and whatnot. Based on Java, this tool runs in an like shooting fish in a barrel-to-apply graphical interface with lost customization options while scanning.
eight. Social-Engineer Toolkit:
It is an advanced framework for simulating multiple types of social engineering attacks like credential harvestings, phishing attacks, and more.

Information technology automates the attacks and generates disguising emails, malicious web pages, and more.
nine. Nessus Vulnerability Scanner :
Nessus is a proprietary comprehensive vulnerability scanner which is developed by Tenable Network Security.

It is free of charge for personal use in a non-enterprise environment. Nessus allows scans for
- Vulnerabilities that allow a remote hacker to control or access sensitive data on a system.
- Misconfiguration (e.g. open mail relay, missing patches, etc.).
- Default passwords, a few mutual passwords, and blank/absent passwords on some system accounts. Nessus can also call Hydra (an external tool) to launch a lexicon assault.
- Denials of service confronting the TCP/IP stack past using malformed packets
- Preparation for PCI DSS audits
Virtually of the globe is using Nessus to audit business-critical enterprise devices and applications.
x. Nessus Remote Security Scanner:
Information technology was open-source only recently information technology has been changed to closed source. It is the most used Security Scanner in over 75,000 organizations worldwide.

Most of the world is using Nessus to inspect business-critical enterprise devices and applications.
11. Kismet:
Kismet differs from other wireless network detectors in working passively. Namely, without sending whatsoever loggable packets, it is able to detect the presence of both wireless admission points and wireless clients and to acquaintance them with each other.

Information technology is likewise the most widely used and up-to-appointment open up-source wireless monitoring tool. likewise includes basic wireless IDS features such every bit detecting active wireless sniffing programs including NetStumbler, as well as a number of wireless network attacks.
12. NetStumbler:
NetStumbler (also known equally Network Stumbler) is a tool for Windows that facilitates detection of Wireless LANs using the 802.11b, 802.11a, and 802.11g WLAN standards.

It runs on Microsoft Windows operating systems. It is used for wardriving, verifying network configurations, finding locations with a poor network, detecting unauthorized access points.
13. inSSIDer:
Information technology is a popular Wi-Fi scanner for Microsoft Windows and Os X operating systems.

It performs diverse tasks which include finding open wi-fi access points, tracking signal strength, and saving logs with GPS records.
Nosotros promise that you establish the best hacking tools for windows. Do let usa know if we missed any on our list.
Source: https://www.alltechbuzz.net/hacking-softwares-for-windows-users/
Posted by: riverafinks1946.blogspot.com


0 Response to "How To Repair Microsoft Hacked Computer"
Post a Comment